Learning could be more like playing a video game
than reading a textbook›››
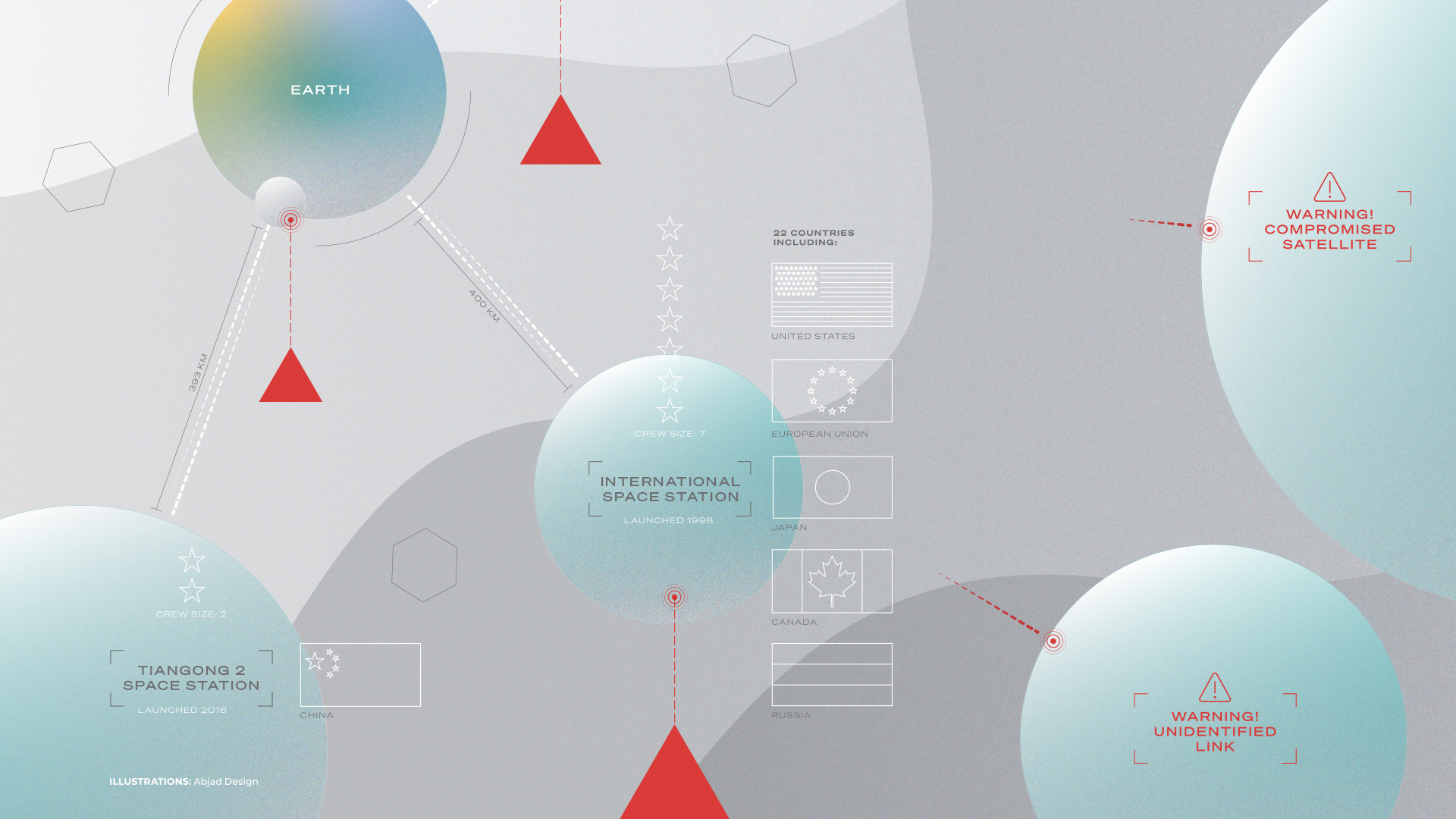
Space was once a domain largely associated with government actions. Sovereign states were solely responsible for sending probes, satellites and crewed missions to Earth’s orbit, the moon and beyond. The technology was similarly segregated: Terrestrial and space systems were generally isolated from each other, creating a kind of “security by obscurity.”
In recent years, however, private industry has launched into space, providing satellite services for telecommunications to the Earthbound that are projected to become a U.S.$1.4 trillion market by 2030. These systems in space talk to the systems on the ground, and the scope is only growing. Cellphone users of tomorrow, for example, may be able to tap into satellites to seamlessly send messages when there is no terrestrial connectivity. Elon Musk’s Starlink is a good, live example.
Listen to the Deep Dive
The World Economic Forum also points out that modern systems establish interfaces across “traditional trust boundaries,” such as partners and customers. And more complex systems have more potentially exploitable attack surfaces.
With such growth and Earth-space network interconnectivity amid such other sectors as the military, aviation, emergency services and utilities, however, comes risk from those who might use those connections to steal, extort, sow chaos or wage war.
Real-world examples
A series of cyberattacks in 2022, for example, targeted three wind farms operated by Germany-based companies. A ransomware group supporting the Russian government said it was responsible for one of the attacks.
Christoph Zipf, a spokesman for WindEurope, a Brussels-based industry group, sees links to the Russia-Ukraine war.

Matthias Brandt, director of Deutsche Windtechnik, which maintains wind turbines and was one of the companies hacked, tells the Wall Street Journal that the renewable-energy sector will become an even more attractive target.
“We need high IT security standards,” he says.
Earlier the same year as the conflict unfolded, another attack linked to hostilities in the region targeted satellite modems, knocking out internet service in Ukraine and other parts of Europe for tens of thousands.
Ukrainian cyber official Victor Zhora called the hack “a really huge loss in communications in the very beginning of the war,” CNN reports.
In response, SpaceX, which created the Starlink network of 3,335 active satellites, shipped truckloads of Starlink terminals to Ukraine in April 2022, providing hospitals, banks and families with internet access. The military also used the network, prompting Starlink to curb the country’s use of the satellites for offensive drones.
By April 2023, the Washington Post was reporting on classified U.S. intelligence that concluded Russia was far more advanced in its plans to target the Starlink network than previously thought.
Additionally: “Starlink usage in Ukraine has been associated with Starlink users’ uplink transmissions becoming beacons for airstrike,” says Christina Pöpper, a professor of computer science at New York University-Abu Dhabi who focuses on information and communications security.
Space, it seems, has become an active theater in Earth conflicts. And the cyberattacks in this conflict could be a harbinger of many more such attacks to come.
Even nations not involved in war have reason to be wary of cyberattacks in space, Pöpper tells KUST Review. “(They) can have far-reaching implications, affecting various aspects of the lives of everyday people from communication and navigation to personal privacy, safety, economic stability and national security.”
3 kinds of attacks
Governments or rogue elements could target satellite systems in a number of ways.
They can target services, rather than the satellites themselves, by hacking and GPS spoofing, as seen in the Ukraine conflict, denying millions access to essential services.
They could also use anti-satellite weapons (ASATs) to target satellites in orbit.
Juliana Suess is a research analyst and policy lead for space security at the Royal United Services Institute, a defense and security think tank with headquarters in London.
“ASAT attack consequences range from temporary and reversible to permanent and non-reversible,” she tells KUST Review.
“The potential consequences are numerous. It needs to be borne in mind that a space system is made up of three basic elements — the satellite in space, the ground station on Earth and the links in between. All three are potentially vulnerable to attack.”
“For example, an adversary may take control (permanently or temporarily) of a satellite through hacking,” Suess says. “They may also disrupt (jam) or spoof the signal reaching or emanating from the satellite with temporary effect. A counterspace measure may also be to prevent a satellite from collecting information — for example by dazzling the sensors onboard of an Earth Observation satellite.”

China, India and Russia have been criticized for testing physically destructive ASAT weapons on their own satellites. But such tactics are expensive, don’t guarantee success and can add to the growing problem of space debris.
The United Nations has approved a non-binding resolution calling for a halt to testing one type of such weapons, the debris-generating direct-ascent ASATs. It cited environmental issues and a desire to prevent an arms race in space. By April 2023, 13 countries, including the United States, Japan and Germany, had pledged to ban the tests.
“Space is difficult,” say Oxford University researchers in a paper published in IEEE. “A launch program alone does not guarantee the resources and precision required to operate a meaningful ASAT capability.”
And then there are cyber-ASATs.
These, the Oxford researchers say, “threaten the foundations of space’s longstanding stability due to their high accessibility, low attributability and low risk of collateral damage.”
In other words: They’re easy to use, hard to pin on the offender and probably won’t damage nearby satellites.
Without firing a rocket, the researchers say, belligerents could alter debris-collision forecasts to cause direct harm to space systems.
“Cyber-ASATs are not merely a distant theoretical threat, but a real and present danger to the balance of power in space.”
Multiple threat vectors
Threats, however, can be hybrid, warns NYU-AD’s Pöpper.
“In reality, multiple threat vectors are often combined,” she tells KUST Review. “Hacking and spoofing are part of cyber anti-satellite weapons. We are dealing with whole infrastructures, so while spoofing satellite (GPS or other) signals typically happens during communication, hacking targets the satellites and satellite operation software, and cyber ASATs also encompass attacks (e.g., exploiting vulnerabilities) on ground control systems.
“Successful attacks can disrupt satellite communications, compromise control systems, manipulate data, and even disable satellites, potentially leading to loss of control, compromised missions, and significant disruptions to various sectors relying on satellite services.”
A good defense
So what are governments and businesses doing about the threat?
“There are a few defenses that can protect satellites — ranging from ‘bodyguard’ satellites (currently in the planning stage) that could accompany sensitive assets to simpler measures such as cyber defenses against hacking,” says space-security expert Suess.

Pöpper, meanwhile, sees three tracks of interest:
Develop and deploy secured space systems: “Recognize that space security is a real problem and thus support the development and deployment of secure space infrastructure, secure communication channels, integrity of satellite firmware and software, and satellite system hardening. There are many open research questions in this domain as well,” she says.
Collaborate and share information: “Share threat intelligence, best practices and lessons learned from previous cyber incidents to enhance the overall security of satellite systems.”
International cooperation and regulations: “Governments should collaborate internationally to establish common cybersecurity standards and regulations for space systems, promoting consistent security practices and enabling a coordinated response to cyber threats. I am aware that this can be a tricky ask beyond national boundaries, but the space industry in general has a long history of multi-national collaborations.”
His Excellency Dr. Mohamed Al Kuwaiti, head of cybersecurity for the UAE, also sees the need for governments to work with businesses and other stakeholders.
“Cybersecurity is teamwork,” he tells KUST Review, “and we have to involve everyone including government entities, industrial partners, academia and the community. That should be done at national and international levels.”



